Web3 Privacy Tools: The State of 2026

Why Rubic Is Entering Privacy
With blockchain adoption and transparency accelerating, we’re entering the privacy era of Web3.
There’s an abundance of privacy tools, but the landscape is highly fragmented and complex. Navigating privacy solutions now feels like navigating blockchains a few years ago: scattered options, unclear differences, and too many decisions just to make a single swap.
Rubic has already simplified cross-chain trading. Now we’re doing the same for privacy.
Our goal is straightforward: educate and navigate users around various privacy tools, and make private swaps and transfers as easy and intuitive as regular ones, without forcing users to become privacy experts.
Read Rubic’s Manifesto to learn more about our vision.
Why There Is A Need For Privacy
“Privacy is an important guarantor of decentralization: whoever has the information has the power, ergo we need to avoid centralized control over information.”— Vitalik Buterin, Ethereum co-founder, “Why I Support Privacy”
The underlying promise of web3 is autonomy and ownership. Privacy sits right there in the middle of that promise.
Once someone has your wallet address, they can see the entire history tied to it, which assets moved where, how much was sent, and when it happened. They can view your transaction metadata, current balances, and recent activity.
From there, it’s not hard to connect that wallet to your social accounts, piece together your trading strategy, and form a pretty detailed picture of your financial behavior.
They can also:
- Track how early you enter new tokens.
- Estimate your portfolio size and risk appetite.
- Monitor when you move funds to exchanges, often a signal you might sell.
- Identify which protocols or tools you prefer using.
- Notice salary payments, DAO rewards, or client transfers if you reuse the same wallet.
- Map connections between your wallets, friends, or business partners, as well as your social accounts.
Over time, a single public address can turn into a full behavioral profile, not just what you own, but how you think, when you act, and where you’re likely to move next.
Several forces are pushing the privacy market forward.
- Surveillance, transaction tracking, and the demand for anonymity are the most obvious. As analytics platforms like Arkham grow more sophisticated, users become increasingly aware of how exposed they and their trading strategies are.
- Privacy is existential for DeFi to scale into TradFi.
- Then there’s regulatory pressure. It drives demand for compliant privacy tools, solutions that enable confidentiality and selective disclosure rather than total opacity.
For most users, the reasons to use privacy solutions are surprisingly practical. It’s not about hiding anything illegal. Wallet tracking has become almost a sport. There are bots, dashboards, influencers analyzing “smart money.” Useful? Sure. Comfortable? Not really.
Banks give you privacy by default, and that doesn’t mean you’re doing anything wrong. Privacy must be a standard, not a feature.
Understanding the Privacy Stack
When you interact with a blockchain, every action passes through multiple layers, and each layer exposes different types of data. To build real privacy, you have to understand where information leaks and where protection can be applied.
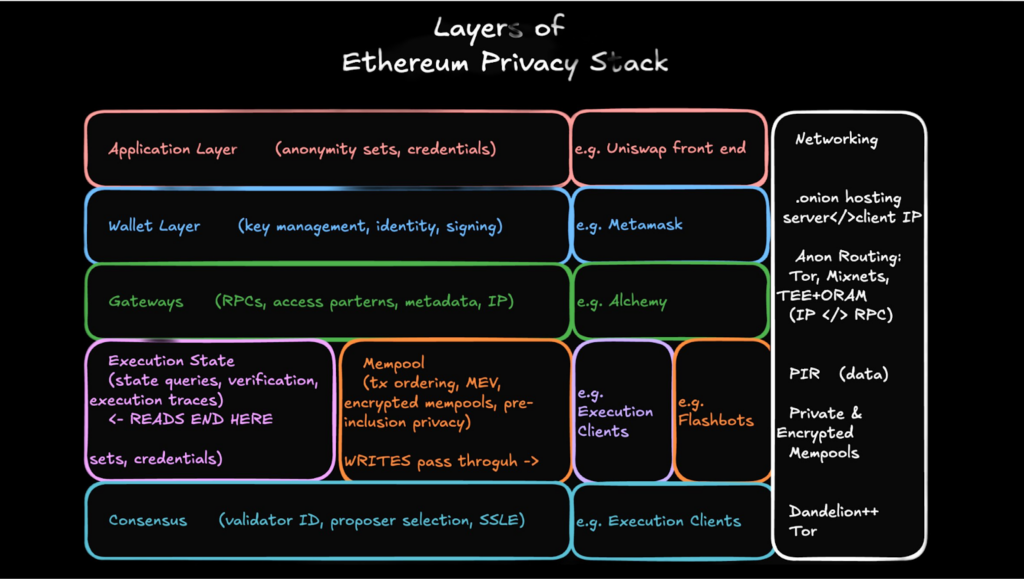
Source: “If you peak, you leak” by Andy Guzman, PSE, The Ethereum Foundation – ETHDenver, 2026
Protecting just one layer doesn’t remove the risk. A transaction can use zero-knowledge proofs and still leak information through a wallet, an RPC endpoint, or even basic networking infrastructure.
Different projects solve different parts of the stack. Some shield balances and transfers. Others focus on private computation, encrypted smart contracts, identity protection, or confidential routing.
“Private” doesn’t always mean fully protected. Often, it means one layer is secured — while others can still remain exposed.
The Privacy Market Landscape
The crypto privacy tools have grown quietly but steadily. They don’t always make front-page headlines like meme coins or AI tokens, but the infrastructure keeps expanding.
A. Compliant Privacy Solutions:
Compliant privacy solutions are tools that protect user privacy without breaking regulatory rules. Unlike mixers or tumblers that aim to hide transactions entirely, compliant solutions balance privacy with transparency where it matters.
What compliance means in crypto privacy:
In this context, compliance generally refers to adhering to legal and regulatory requirements while still protecting sensitive data:
- AML/KYC alignment: satisfy AML laws if required.
- Auditable trails without public exposure: It allows for inspection by authorized parties without exposing private user activity to everyone.
- Regulatory transparency: You can prove the legitimacy of your funds or transactions, and lower legal risks.
Compliant privacy solutions often use:
- Zero-Knowledge Proofs (ZKPs): proving something is true without revealing the underlying data.
- Stealth addresses: hiding sender or receiver details.
- Confidential transactions: masking transaction amounts while still verifying validity.
- Selective disclosure/viewkeys: Auditors or regulators can see transaction information if necessary, without exposing it publicly.
Examples
Protocols and networks that integrate ZK-based privacy layers, confidential transfer mechanisms, or selective disclosure systems fall into this category. Some operate as entire privacy-focused chains, others as modules on existing ecosystems.
ZCash, Zama, Houdiniswap, Oasis Network, Privacy Cash, Hinkal Protocol.
B. Mixers (Tumbling Services)
Mixers are the more controversial side of crypto privacy. Providing a high level of anonymity, they’ve been around for years and have seen waves of popularity followed by waves of scrutiny.
Definition & Mechanics
A mixer pools together funds from multiple users, shuffles them, and redistributes them so that original transaction paths become difficult, sometimes nearly impossible, to trace. It’s like putting coins into a large jar, shaking it, and taking different coins out. Simple concept, complex implications.
Examples
Various centralized and decentralized tumbling services have existed across Bitcoin and Ethereum ecosystems, though many have faced shutdowns, sanctions, or legal actions.
TornadoCash, ChipMixer, Samourai Wallet.
Rubic’s Position
Rubic is pioneering crypto privacy aggregation. That means we’re committed to educating and guiding users through this complex landscape.
By bringing multiple solutions into one interface, we simplify decision-making and better serve user needs. Whether that’s cost (private transactions can be costly, depending on the protocol), speed (shielding takes time), or privacy level, the suitable route is on Rubic.
Historically, we specialize in interoperability. Users on private chains often hesitate to move assets elsewhere because bridging can reveal transaction histories. Rubic addresses this friction by focusing on routing and aggregating various privacy solutions that can minimize exposure risks.
Our focus is on compliant privacy. Rubic does not require KYC, while the protocols we aggregate are built to function within regulatory frameworks, delivering discretion without stepping outside compliance boundaries.
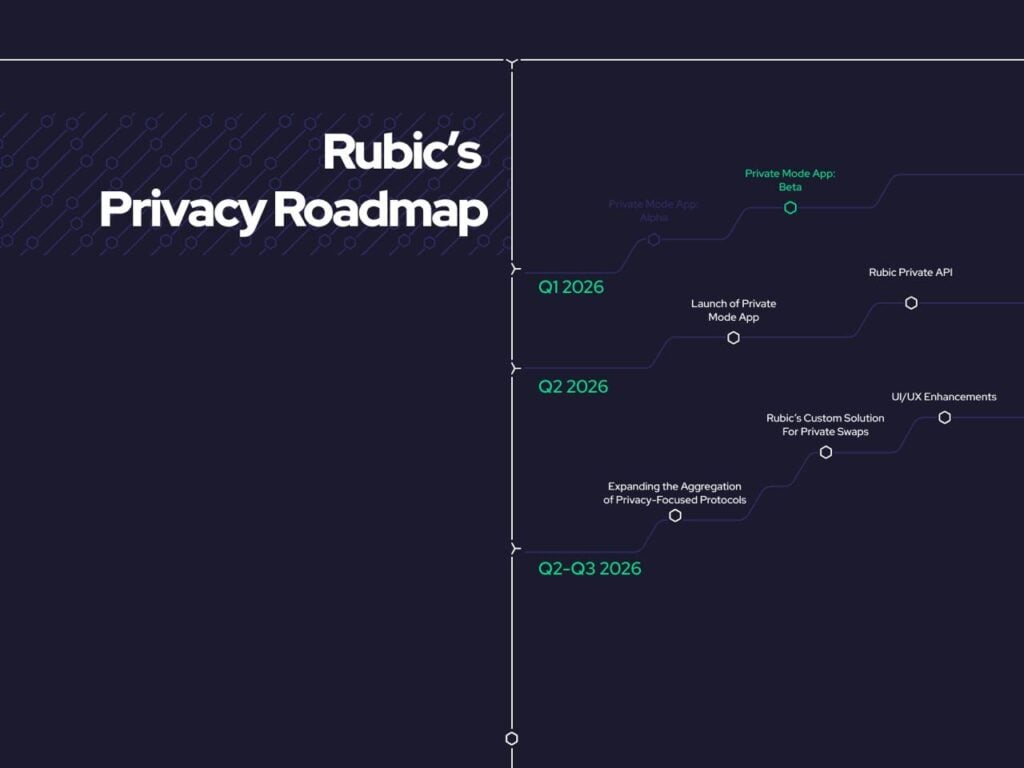
Our first step is aggregating Zama, Railgun, Hinkal Protocol, Privacy Cash, ClearSwap and Houdini Swap.
Next, we’ll expand the aggregation of privacy solutions and develop a privacy aggregation API. We’ll continue refining user experience, making it simple and intuitive for anyone to interact with privacy tools.
How Privacy Works: The Tech Behind the Scenes
| Technology | What It Is | Crypto Use Case | What It Hides |
| Zero‑Knowledge Proofs (ZK / ZKPs) | A cryptographic method that lets you prove something is true without revealing the actual information. | You can prove a transaction is valid, that you own funds, or that rules were followed, without revealing balances, addresses, or amounts.Often used in privacy chains and zk‑rollups. | Amounts, balances, identities (depending on implementation). |
| TEE: Trusted Execution Environment | A secure area inside a computer or server where data can be processed without the outside world seeing it. | Used to run private computations, routing, or order matching without exposing user data publicly. | Raw data during processing (not necessarily on-chain history). |
| FHE: Fully Homomorphic Encryption | Encryption that allows computations to be performed directly on encrypted data without decrypting it first. | By allowing smart contracts to operate on confidential data, FHE facilitates private transactions, confidential DeFi, and secure, trustless computation. | Everything: inputs, outputs, and intermediate data. |
| Stealth Addresses | A system that generates a one‑time address for every transaction even though the recipient uses one public wallet. | Prevents outsiders from linking multiple payments to the same receiver. | Recipient identity and transaction linkage. |
| Ring Signatures | A digital signature that mixes your signature with several others, making it impossible to know which member actually signed. | Used to hide the sender of a transaction. | Sender identity. |
| RingCT: Ring Confidential Transactions | An extension of ring signatures that also hides transaction amounts. | Common in privacy‑focused blockchains. Combines sender anonymity + hidden amounts. | Sender + amount. |
| Multi-Party Computation (MPC) | Allows multiple parties to jointly compute a function without revealing their individual inputs. | Can be used for private wallets, key management, and decentralized private smart contracts. | Individual inputs, private keys, and transaction logic, computations happen without exposing the underlying data. |
| Viewkeys & Selective Disclosure | Special keys that let authorized parties (auditors, regulators, or yourself) see transactions without exposing them publicly. | Balances privacy with compliance needs. | Transaction details from the public while allowing selective access for authorized viewers. |
Privacy-Focused Tools
The privacy landscape isn’t easy to navigate. The technology behind each tool is different. Some solutions route through CEXs, while others are fully decentralized. Execution times vary, one swap might take two minutes, another five or more. Fees vary by protocol, and each solution supports its own set of tokens and networks.
Comparing all of this manually can quickly become overwhelming. That’s exactly why we aggregate them on Rubic, so users don’t have to analyze every route, cost, and limitation themselves.
Below, we’ve compiled an overview of the leading privacy tools on the market.
Privacy-Focused Chains
These are blockchains designed from the ground up to protect transaction data, balances, and identities.
Purpose: Hide sender, receiver, and transaction amounts by default.
What it hides: Wallet addresses, transaction amounts, and activity patterns.
| Chains | EVM/non-EVM | Technology | Use Cases |
| Monero | non-EVM | Stealth Addresses, Ring Signatures, RingCT | Private and confidential transactions |
| Zcash | non-EVM | ZK | Selective disclosure and compliance |
| Secret Network | non-EVM | TEEs, privacy-preserving smart contracts. | Hold and use your tokens in privacy. |
| Oasis | EVM | TEEs, strong cryptography, light client verification, VRFs, MPC protocols and distributed consensus | Private and confidential transactions |
| Aztec | EVM | L2 ZK rollup | Private and confidential transactions, privacy-preserving KYC |
| Canton | non-EVM | Sub-transaction level privacy, “Proof-of-Stakeholder” consensus | Parties can only see the part of a transaction that specifically applies to them |
| Miden | EVM | ZK | Selective disclosure and compliance |
| Aleo | EVM | ZK | Private and confidential transactions, privacy-preserving KYC |
| Dusk | EVM | ZK | Anonymous, yet compliant, trading; compliant asset tokenization |
| Iron Fish | non-EVM | ZK | Private and confidential transactions |
| Coti | EVM | Garbled Circuits encryption | Confidential transactions, confidential DeFi, private voting, private RWA tokenization |
| Mina | EVM | ZK | Permissionless web oracles, privacy-preserving KYC |
| Dash | non-EVM | PrivateSend (Mixer) | Private transactions |
| Arcium | EVM | combining MPC, FHE, and ZKP | Private DeFi: Dark pools & private order books, private lending & borrowing |
| Beldex | non-EVM | (Monero fork: RingCT, Stealth Addresses), FHE | Private and confidential transactions |
| Firo | non-EVM | Lelantus Spark ZK protocol | Private and confidential transactions |
| NIL | Testnet | ZK | Private and confidential transactions |
| Midnight | Testnet | ZK | Private voting, private KYC, private DeFi |
Privacy-Focused Protocols
Privacy-focused protocols enable dApps to operate with added privacy layers.
Purpose: Enable private transactions or private smart contracts.
What it hides: Transaction paths, amounts, and smart contract inputs/outputs.
| Project | Chains | Technology | Use Cases |
| Railgun | Ethereum, Polygon, BSC, and Arbitrum | ZK SNARKs | ZK proofs of non-interaction, private transfers, shielding any ERC-20 or NFT into any 0zk private address |
| Zama | EVM-chains | FHE | Private DeFi, payments, banking, tokens, RWA-tokenization, sealed-bid auctions |
| 0xbow | EVM-chains | Privacy pools | P2P private transactions |
| Hinkal | Ethereum, Polygon, OP, Base, and Arbitrum | ZK proofs, stealth addresses, TEEs | Private storage, transfers, and dApp interactions on public chains |
| Fhenix | Ethereum | FHE | Private DeFi, encrypted trades on Uniswap |
| Panther Protocol | EVM-chains | ZK | Private transactions in Shielded Pools, confidential portfolio management |
| Silent Protocol | In Private Beta | ||
| Lumenless (ex Light) | Solana | haven’t launch yet | Private payments. Private trading. |
| ZeraLabs | Solana | ZK | Shielded balances, private transfers |
| Cloak | Solana | ZK proofs, relay submission, and PoW-secured delivery | Private transfers, continuous wallet risk analysis |
| Umbra | Solana | MPC, ZK proofs, powered by Arcium | Private transfers |
| Kohaku | Ethereum | Modular privacy SDK | Open-source wallet SDK and reference implementation for developers on Ethereum to build private-by-default wallets |
Privacy-Focused dApps
dApps that prioritize user confidentiality in trading, lending, or swapping.
Purpose: Let users interact with DeFi platforms while keeping balances, trades, and strategies hidden.
What it hides: User activity, trading strategy, and financial behavior.
| Project | Chains | Technology | Use Cases | Fees + Swap Execution Time |
| Houdini | 124 chains | CEX pools interact with a randomly selected Layer 1 token which acts as a privacy layer severing any connection between them | Private transactions, private payments | Fees: 0.8% Swap Execution Time: up to 20 minutes |
| RocketX | 200+ | Split-Route Execution via CEXs | Private transactionsWalletless swaps | Fees: 0.4%Swap Execution Time: up to 10 minutes |
| SilentSwap | 37 chains | Shielded transfers, TEE, private pools | Private transactions | Fees: ~1%Swap Execution Time: up to 5 minutes |
| Privacy Cash | Solana | ZK proofs, an append-only Merkle tree, and a relayer system | Private Solana transfers and swaps | Fees: – 0.35% of withdrawal amount- 0.01 SOL network and rent fee- Jupiter Swap fees determined by Jupiter Swap Execution Time: up to 5 minutes |
| Peer | EVM-chains | ZK proofs | Private on/offramp, private transfers | Social loginFees: lowSwap Execution: near-instant |
| TurbineCash | Solana | Merkle tree, ZK proofs | Private DCA, private transfers | Fees: 0.30%Swap Execution Time: ~Instant |
| Encrypt.trade | Ethereum, Tron, Base, ZCash, Polygon, Monad and Arbitrum | Encrypted versions of tokens (eTokens) using threshold ElGamal encryption | Private swaps on Jupiter, private send | Fees: 0.5%Swap Execution Time: up to 10 minutes |
| PoseidonCash | Solana | ZK shielded transaction, zkSNARKs and a Merkle tree | Private p2p token swaps, private transaction soon | Preparing for mainnet launch |
| Vanish | Solana | Vanish’s shielded execution layer | Shielded transactions to Solana | Fees: ?Swap Execution Time: up to 10 minutes |
| NullTrace | Solana | ZK Proofs | Private transactions, private transfer | Fees: 0.1%Swap Execution Time: up to 10 minutes |
| DarkLake | Solana | ZK proofs | Private transactions | Fees: 0.5%Swap Execution Time: up to 10 minutes |
| Renegade | Arbitrum, Base | ZK proofs, MPC, dark pools | Private on-chain swaps | Fees: 0% protocol fee and 0.02% relayer feeSwap Execution Time: up to 10 minutes |
| ClearSwap | TRON | Dual Exchange System via semi-centralized provider + Randomized L1 | Private on-chain swaps | Fees: Up to 2.5% |
Privacy-Focused Wallets
Wallets that integrate privacy tools directly, so sending, receiving, or storing crypto doesn’t expose data unnecessarily.
Purpose: Make private transactions simple and accessible.
What it hides: Sender/receiver links, transaction history, balances, and sometimes even usage patterns.
| Project | Chains | Technology | Use Cases | Onboarding Simplicity 1-5 (1 = the simplest) |
| Hush(Browser Extension) | Solana | ZK proofs and a multi-wallet architecture | Send privately: SOL withdrawals from the shielded pool have no on-chain link back to youSwaps: Jupiter-powered swaps with automatic shielding when swapping to SOLBurner wallets: Every receive generates a fresh one-time address that self-destructs after useDApp wallets: Standalone wallets for connecting to dApps without exposing your main walletZCash bridging: Native cross-chain bridging via NEAR Intents | 2 |
| Ambire Wallet (Browser Extension) | EVM-chains | Account abstraction, EIP-7702 | Cross-chain swapsMulti-address privacySend/receiveGas abstraction | 1 |
| Railway(Desktop Wallet) | Ethereum, Arbitrum, Polygon, BNB Chain | Shielding into a private 0zk address | Private transfers, private DeFi, shielded balancesPrivate on-chain swaps (limited tokens + stables) | 4 |
| Zodl (Mobile Wallet) | ZCash | Shielding into a private 0zk address | Private transfers, shielded balancesPrivate swaps from 100+ tokens only to $ZEC, powered by Near Intents | 1 |
| Hinkal Wallet(Browser Extension) | Base, Polygon, Optimism, Ethereum, Arbitrum | ZK proofs, stealth addresses, TEEs | Private storage, transfers, and dApp interactions on public chains, shielded balancesPrivate on-chain swaps (100+ tokens) | 2 |
| Shield (Browser Extension) | Aleo | ZK proofs | Private storage, transfers, and dApp interactions, shielded balancesPrivate swaps from ~10 tokens + stables to $ALEO/$USAD | 3 |
Privacy-Focused Infrastructure
Accommodating technology that enables privacy across chains, protocols, and apps.
Purpose: Provide the building blocks for privacy without compromising usability or compliance.
What it hides: Transaction details, computation inputs/outputs, smart contract logic, and selective data.
| Project | Chains | Technology | Use Cases |
| Arcium | Chain-agnostic | MPC | Confidential DeFiDark Pools |
| Fairblock | Arbitrum, Hyperliquid, Solana, Base, Cosmos | MPC + FHE | Front‑Running & MEV ProtectionPrivate Limit Orders & Intent‑Based TradingConfidential Stablecoin |
| Sunscreen | FHE | ||
| EY | EVM-chains | Compliant-shielded transfers with selective disclosure | SaaS Solutions deliver privacy-enabled blockchain technologies to transform the ways enterprises transact and interact. |
| Shutter Network | Gnosis Chain | Encrypted mempools via threshold encryption | Shielded TradingShielded Voting |
| Flashbots | EVM-chains | TEE-based block building | MEV bot protection |
| zkSync | EVM-chains | zk-SNARKs, obfuscation | Launching EVM-based system |
| NYM | – | Network-level traffic privacy | VPN |
In the end, the privacy market in crypto isn’t a single path. It’s more like a forked road with multiple directions, compliant discretion, cryptographic shielding, full anonymity, hybrid approaches. None of them are perfect. None of them universally trusted either.
And maybe that’s the most human part of it. Privacy isn’t a binary switch. It’s a spectrum, negotiated constantly between visibility and control. Between convenience and caution. Between what we can reveal and what we’d simply rather keep to ourselves. But it’s rapidly developing, and we’re committed to publish more and more information about privacy, making it easy and accessible.
Content Lead at Rubic with a deep dive into Web3 trends, industry narratives, and market analysis


